Out of Band XXE in an E-commerce IOS app

While testing IOS app of the target application, I had found XXE vulnerability for which I’m going to share the writeup. Wanted to publish this since long time, but was only waiting for the disclosure. Anyways, since I did not received permission to reveal the name of the target, I’m going to redact their name in the screenshots.
The target is a big giant in E-commerce industry and their app has more that 50 million downloads as of today.
The vulnerability detection was easy due to the XML parsing error displayed to the end user. The parsing functionality did not had XML External Entity Declaration disabled which allowed an attacker to read files from the server.
About XXE
An XML External Entity attack is a type of attack against an application that parses XML input. This attack occurs when XML input containing a reference to an external entity is processed by a weakly configured XML parser. This attack may lead to the disclosure of confidential data, denial of service, server side request forgery, port scanning from the perspective of the machine where the parser is located, and other system impacts.
Vulnerability Identification
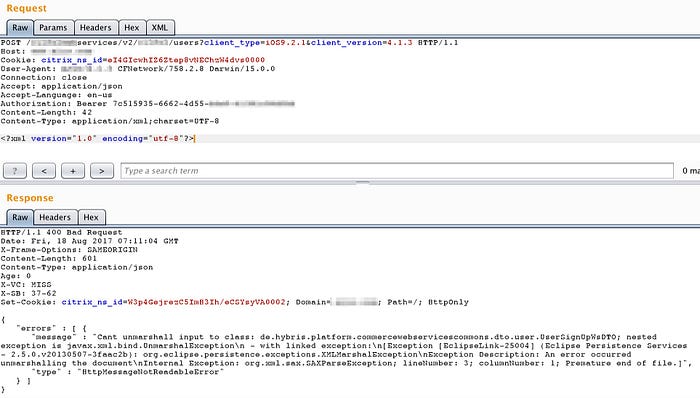
The first identification that the host might be processing XML was made when I flipped the content type to XML on a JSON endpoint.
By sending a generic XML payload, the target returned XML parsing error which confirmed the suspicion that the application was processing XML input.
External Service Interaction
To check whether it was possible to make requests to external sites, I started a listener on the remote server and used XML payload to send a request to that server.
As shown in the following screenshot, the connection was received from the target IP address. Also, the user-agent indicated that the back-end server is processing Java.

Out-of-Band Data Retrieval
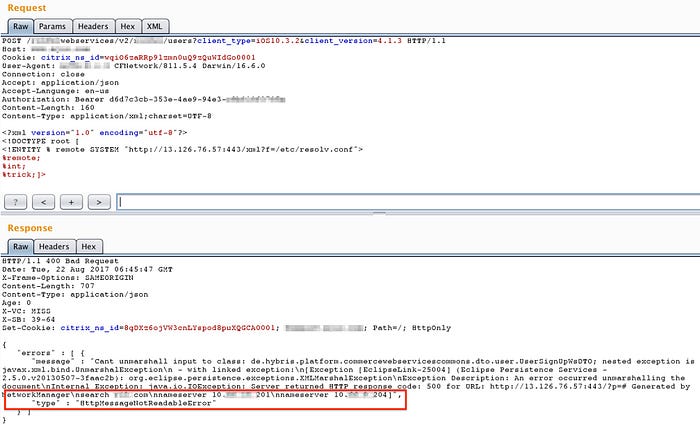
The next thing to do was to exfiltrate data from the remote host.
I used XXEserve in this case which runs a web server, creates a DTD file and prints out the logs. XXEServe is a tiny Sinatra app that runs a server which is useful in collecting data sent out of band.
The following image shows it was possible to retrieve files from the target host (/etc/resolv.conf in the following case) via HTTP using XXEServe.
To harden a JSON endpoint, XML parsing should be disabled altogether and/or inline DOCTYPE declarations should be disabled to prevent XML external entity injections.
The vulnerability was reported and fixed in few hours by the team.
